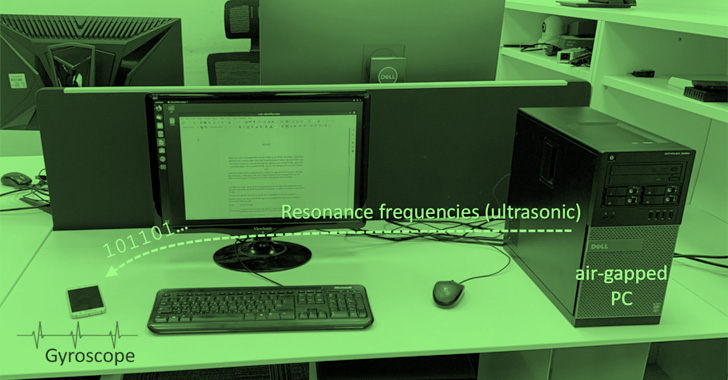
A novel information exfiltration method has been discovered to leverage a covert ultrasonic channel to leak delicate data from remoted, air-gapped computer systems to a close-by smartphone that does not even require a microphone to choose up the sound waves.
Dubbed GAIROSCOPE, the adversarial mannequin is the newest addition to an extended listing of acoustic, electromagnetic, optical, and thermal approaches devised by Dr. Mordechai Guri, the pinnacle of R&D within the Cyber Safety Analysis Middle within the Ben Gurion College of the Negev in Israel.
“Our malware generates ultrasonic tones within the resonance frequencies of the MEMS gyroscope,” Dr. Guri stated in a new paper revealed this week. “These inaudible frequencies produce tiny mechanical oscillations throughout the smartphone’s gyroscope, which will be demodulated into binary data.”
Air-gapping is seen as an important safety countermeasure that entails isolating a pc or community and stopping it from establishing an exterior connection, successfully creating an impenetrable barrier between a digital asset and risk actors who strive to forge a path for espionage assaults.
Like different assaults towards air-gapped networks, GAIROSCOPE is not any completely different in that it banks on the power of an adversary to breach a goal atmosphere by way of ploys comparable to contaminated USB sticks, watering holes, or provide chain compromises to ship the malware.
What’s new this time round is that it additionally requires infecting the smartphones of staff working within the sufferer group with a rogue app that, for its half, is deployed by way of assault vectors like social engineering, malicious adverts, or compromised web sites, amongst others.
Within the subsequent section of the kill chain, the attacker abuses the established foothold to harvest delicate information (i.e., encryption keys, credentials and many others.), encodes, and broadcasts the data within the type of stealthy acoustic sound waves by way of the machine’s loudspeaker.
The transmission is then detected by an contaminated smartphone that is in shut bodily proximity and which listens by way of the gyroscope sensor constructed into the gadget, following which the information is demodulated, decoded, and transferred to the attacker by way of the Web over Wi-Fi.
That is made doable due to a phenomenon known as ultrasonic corruption that impacts MEMS gyroscopes at resonance frequencies. “When this inaudible sound is performed close to the gyroscope, it creates an inside disruption to the sign output,” Dr. Guri defined. “The errors within the output can be utilized to encode and decode data.”
Experimental outcomes present that the covert channel can be utilized to switch information with bit charges of 1-8 bit/sec at distances of 0 – 600 cm, with the transmitter reaching a distance of 800 cm in slender rooms.
Ought to staff place their cell phones shut to their workstations on the desk, the strategy may very well be used to trade information, together with brief texts, encryption keys, passwords, or keystrokes.
The info exfiltration methodology is notable for the truth that it does not require the malicious app within the receiving smartphone (on this case, One Plus 7, Samsung Galaxy S9, and Samsung Galaxy S10) to have microphone entry, thus tricking customers into approving their entry with out suspicion.
The speakers-to-gyroscope covert channel can also be advantageous from an adversarial perspective. Not solely are there no visible cues on Android and iOS when an app makes use of the gyroscope (like within the case of location or microphone), the sensor can also be accessible from HTML by way of normal JavaScript.
This additionally implies that the dangerous actor does not have to set up an app to obtain the supposed targets, and might as an alternative inject backdoor JavaScript code on a authentic web site that samples the gyroscope, receives the covert indicators, and exfiltrates the data by way of the Web.
Mitigating GAIROSCOPE requires organizations to implement separation insurance policies to maintain smartphones at the least 800 cm away or extra from secured areas, take away loudspeakers and audio drivers from endpoints, filter out ultrasonic indicators utilizing firewalls SilverDog and SoniControl, and jam the covert channel by including background noises to the acoustic spectrum.
The examine arrives just a little over a month after Dr. Guri demonstrated SATAn, a mechanism to leap over air-gaps and extract data by making the most of Serial Superior Know-how Attachment (SATA) cables.